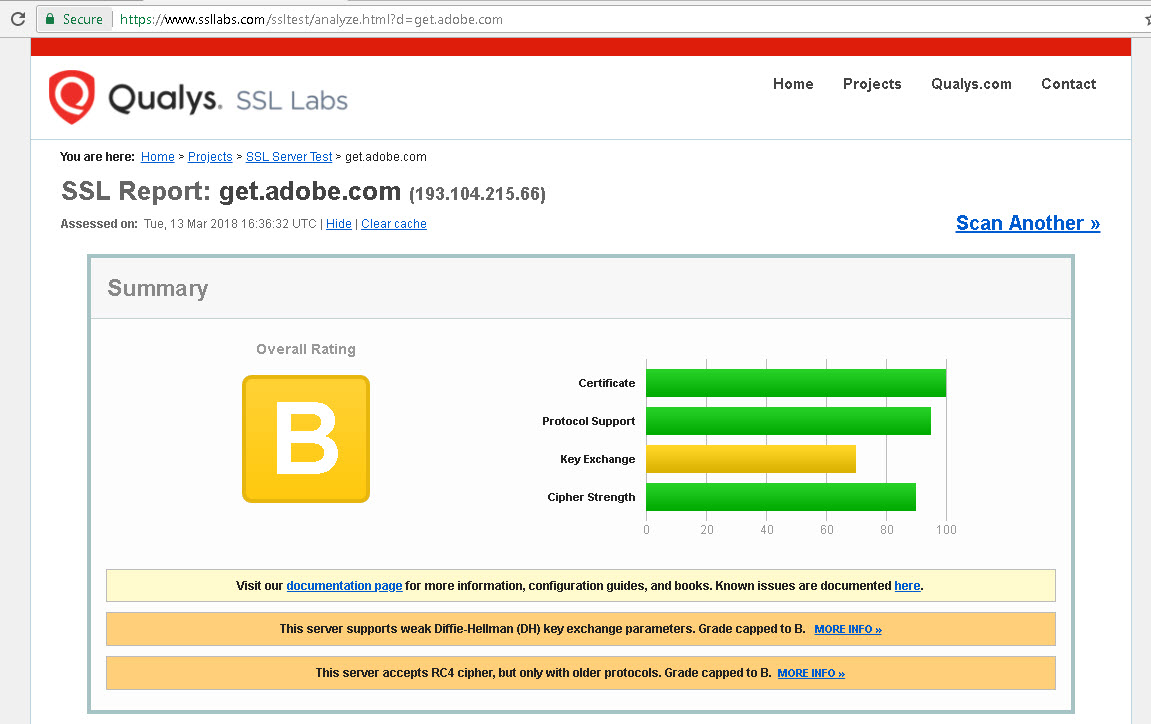
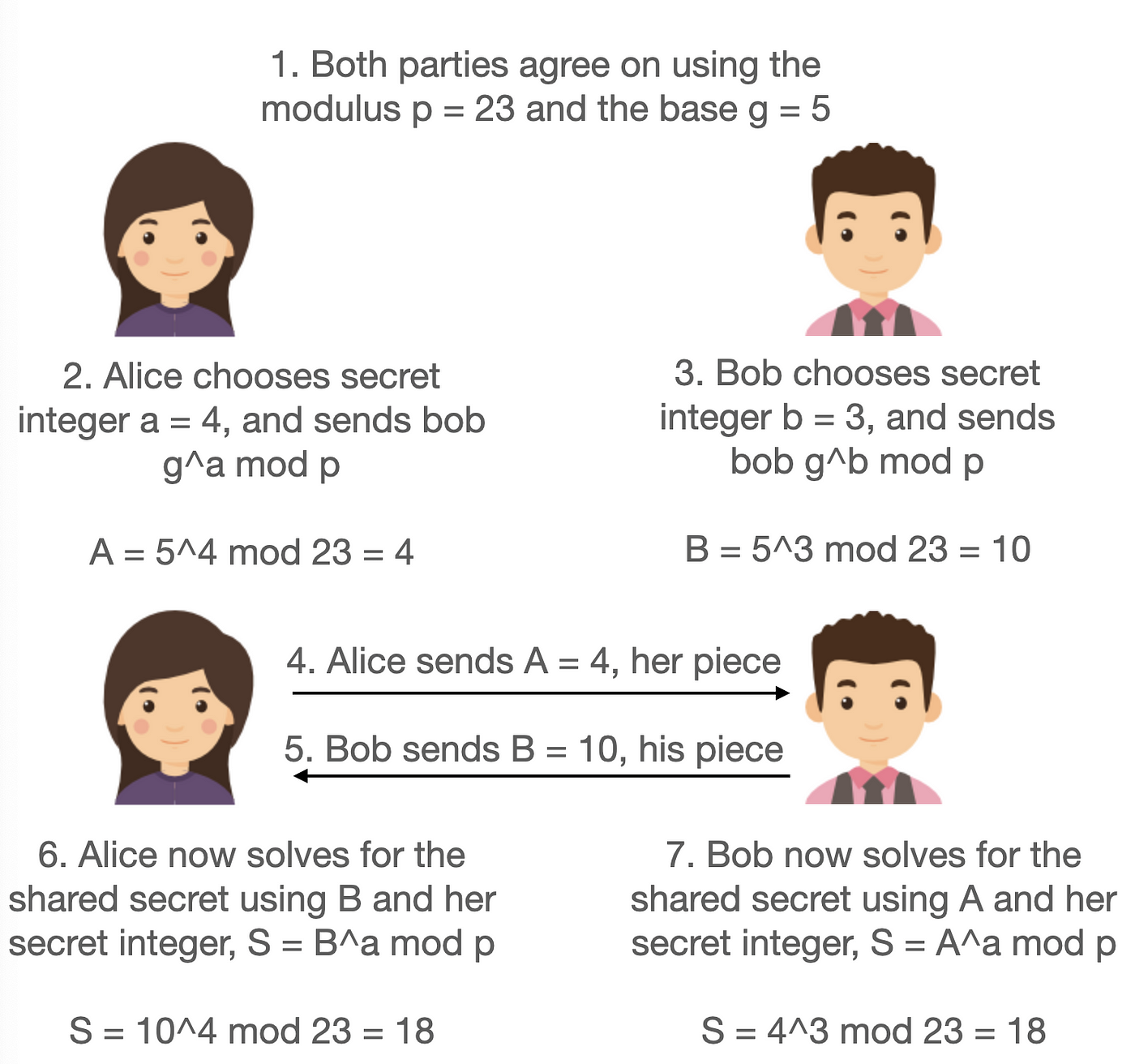
Imperfect Forward Secrecy: How Diffie-Hellman Fails in Practice | January 2019 | Communications of the ACM

Imperfect Forward Secrecy: How Diffie-Hellman Fails in Practice | January 2019 | Communications of the ACM

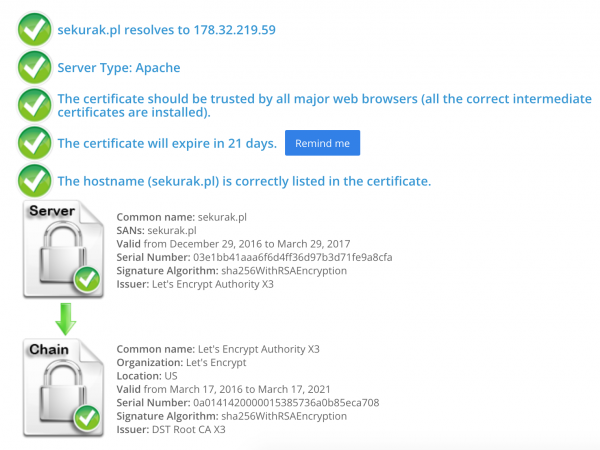
An Internet-Wide Analysis of Diffie-Hellman Key Exchange and X.509 Certificates in TLS | Semantic Scholar