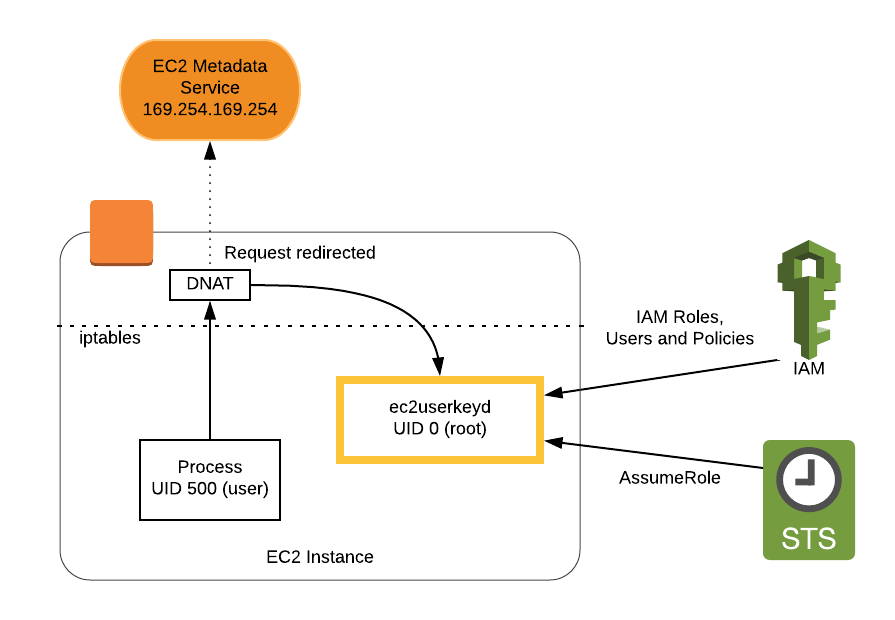
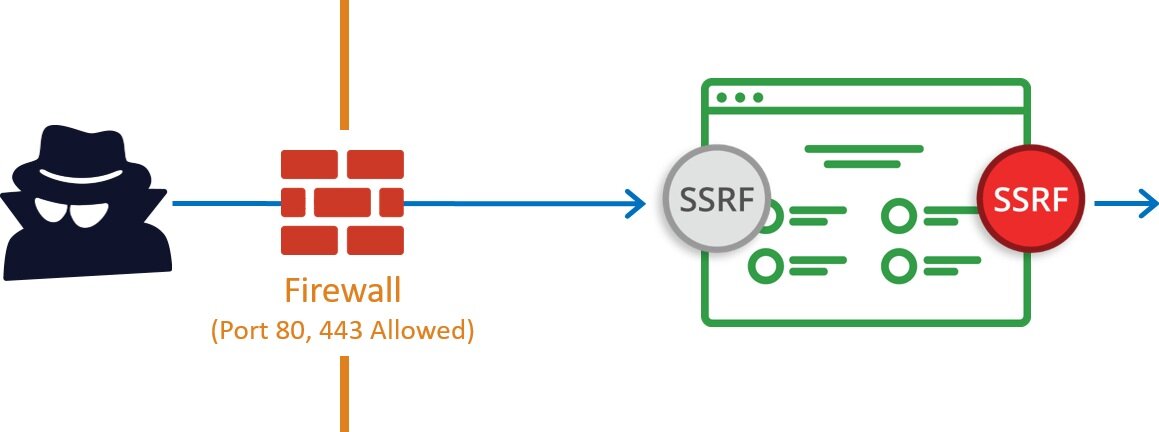
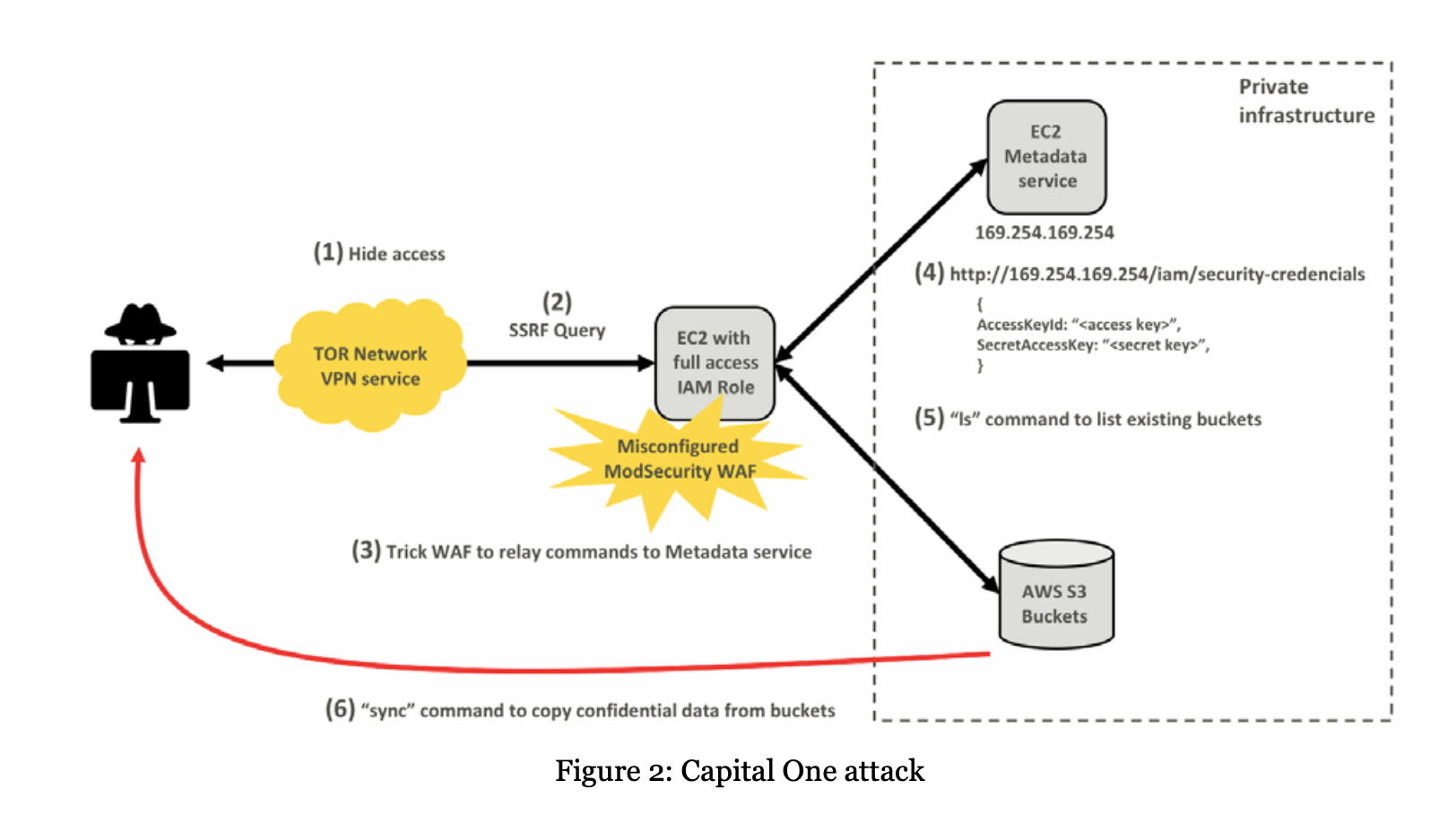
Detecting Server-Side Request Forgery Attacks on Amazon Web Services The ISSA Journal : February 2020

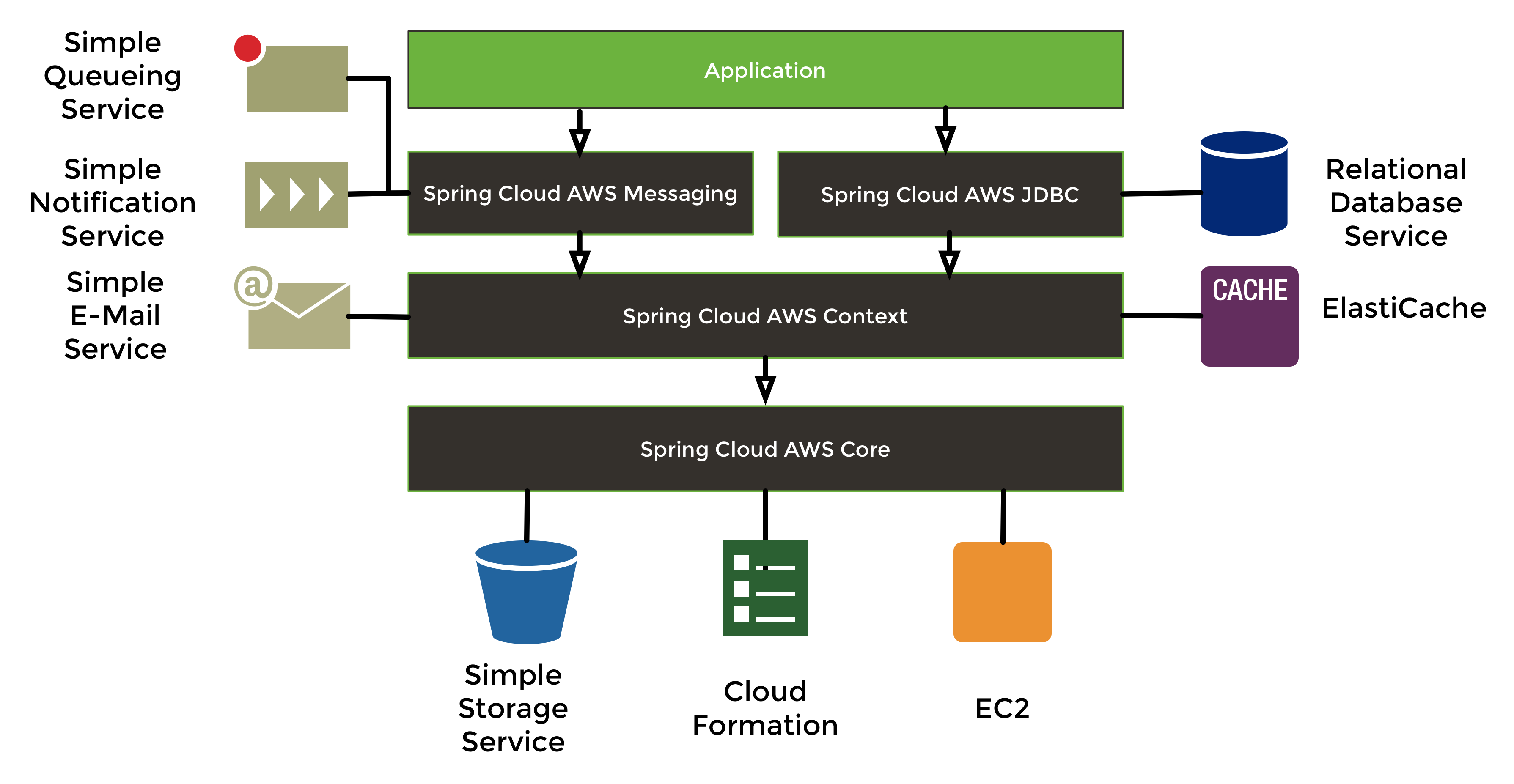
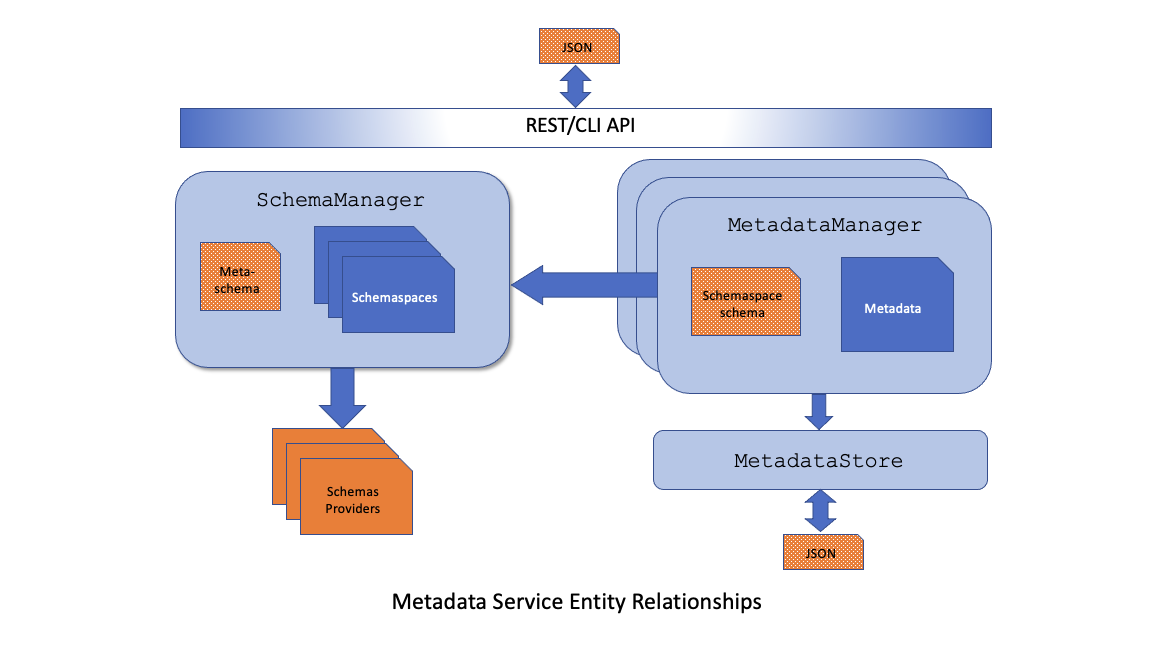
Managing your application metadata using AWS Service Catalog App Registry | AWS Cloud Operations & Migrations Blog
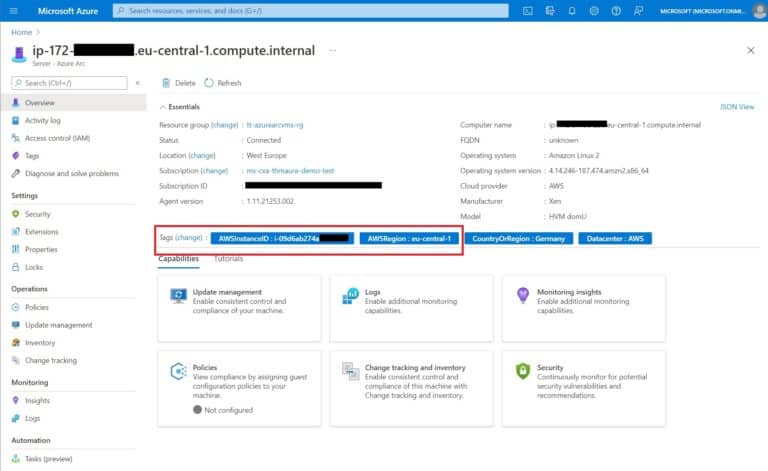
Netflix Cloud Security: Detecting Credential Compromise in AWS | by Netflix Technology Blog | Netflix TechBlog