Secure your data with Amazon RDS for SQL Server: A guide to best practices and fortification | AWS Database Blog
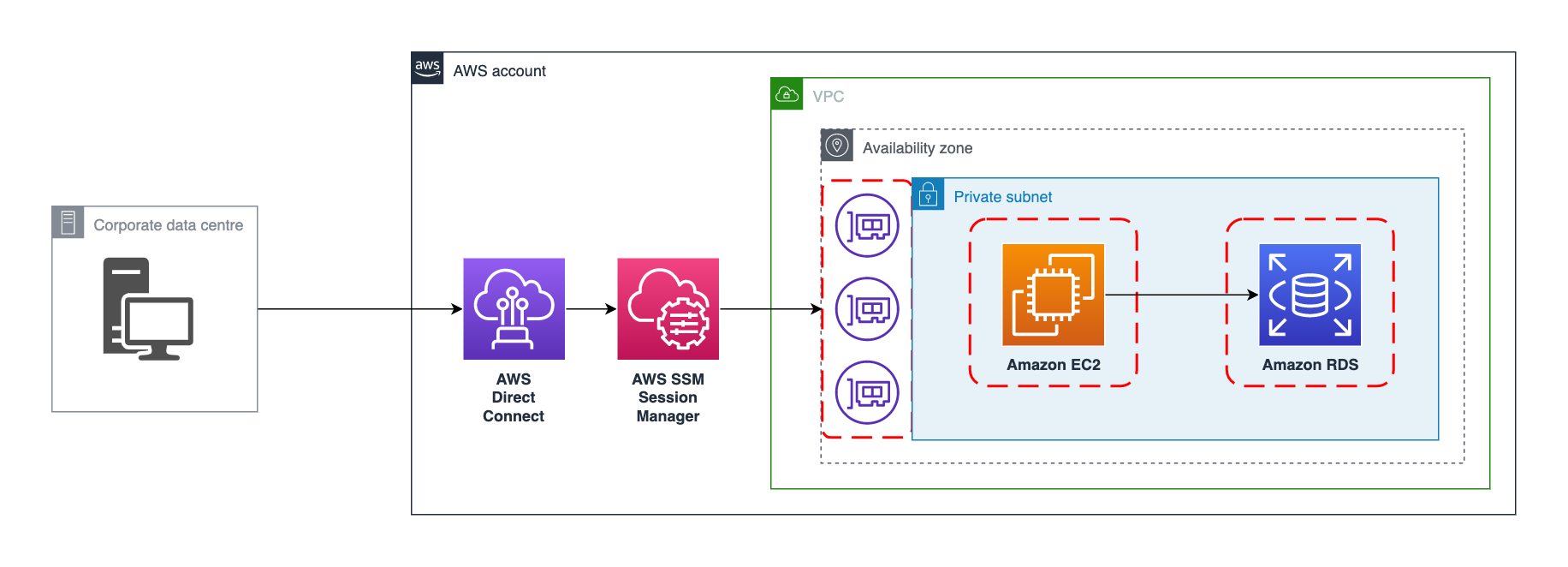
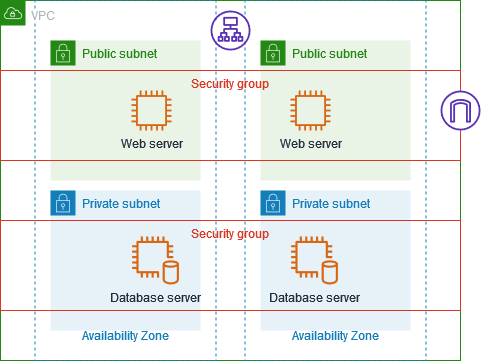
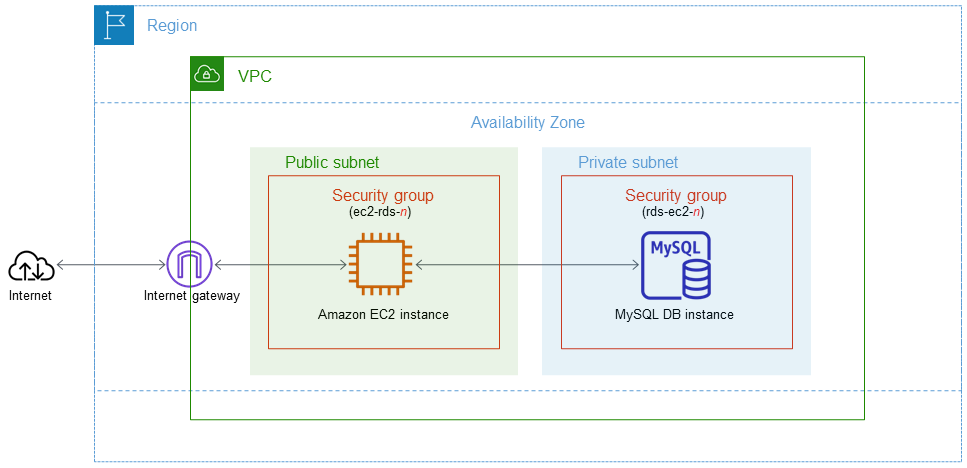
Securely connect to an Amazon RDS or Amazon EC2 database instance remotely with your preferred GUI | AWS Database Blog

Use EC2 Instance Connect to provide secure SSH access to EC2 instances with private IP addresses | AWS Security Blog

Secure Connectivity from Public to Private: Introducing EC2 Instance Connect Endpoint | AWS Compute Blog
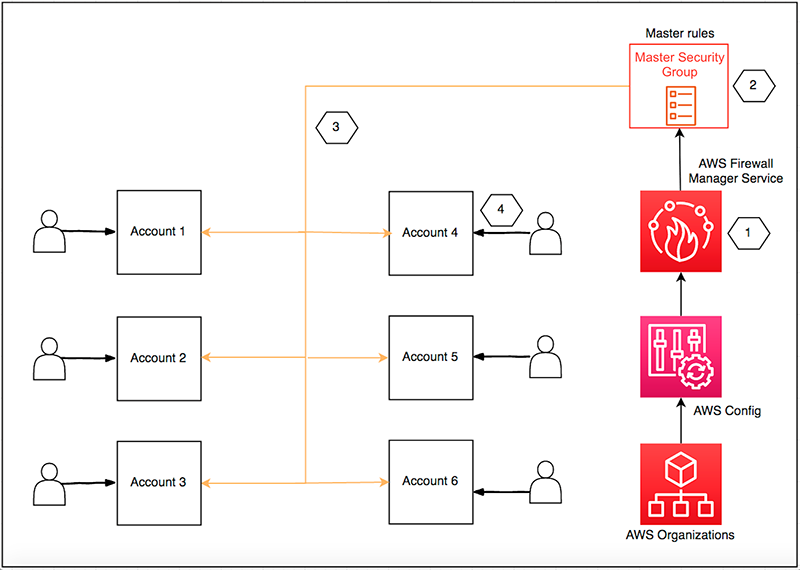
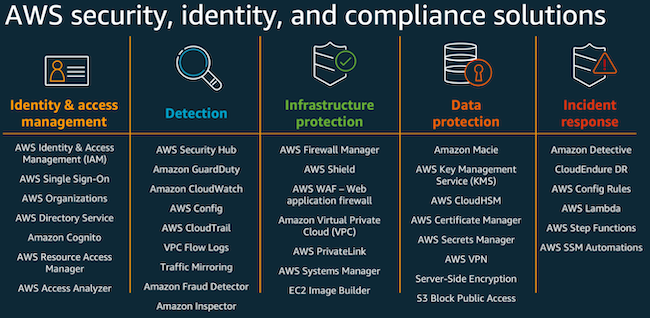
Use AWS Firewall Manager and VPC security groups to protect your applications hosted on EC2 instances | AWS Security Blog